Back to ConfigMgr main menu
Back to MDM Menu
This is a lengthy process and can be a little tricky. I've tried to be as detailed as possible so this is a long post. Note that it can take several days to get a Symantec Enterprise Code Signing Certificate. Be careful and try to get it right first time - it can be a lot of hassle otherwise.
(If you just want to trial this technology then you shouldn't spend the money required below - download the support tool for Windows Intune Trial Management of Window Phone 8)
Note that management of Windows Phone through SCCM 2012 and Windows Intune is only supported on version 8. Previous versions can be managed by using the Exchange connector.
The basic steps are as follows:
1. Windows Developer Account
2. Symantec Enterprise Code Signing Certificate
3. Sign Company Portal
4. Enable Windows 8 Phone
5. Test Windows 8 Phone device
1. Windows Developer Account
The first step in this process is to sign up for a Windows Developer Account. Note that there is a cost associated with this.
You can sign up here
Scroll down
Select "Accept and Continue"
Sign in with your Microsoft account.
This is a highly secure process. An email is sent to you containing a security code. Enter the code.
Choose your region.
Make sure that you choose a Company account.
Enter your details where required (red asterisk).
Choose a "Publisher Display Name". This should be your company name (that can be verified).
Accept the Microsoft Terms and Conditions.
Review your order.
Enter your credit card details.
Click Purchase to order the account.
You're told that "You're done!". This is not quite right. Note that you are told that Symantec will contact you on behalf of Microsoft to verify the account information.
Verify your account information. See "Validating your account". Click "Learn more" for details on this process. Also note your Symantec ID. You will require this later to purchase the Enterprise Code Signing Certificate.
Read and understand the validation process.
Within 15 mins you should receive an email confirming your order. You account is still not validated. This will be a manual process. Symantec (on behalf of Microsoft) must contact you to verify that you have actually placed this order.
Several hours later (5 in my case) you will receive this email from Symantec. It tells you that telephone verification is required and urges you to contact them via Live Chat (link is supplied). Surprisingly it is pretty easy to make contact via Live Chat. You will be answered very quickly and the Symantec rep will make arrangements to call you (notify your switchboard operator that you are expecting this call - they may think it's sales related).
Several hours after the call from Symantec (6 in my case) you will receive an email stating that your identity has been verified by Symantec.
Very soon after you get an email from Microsoft confirming that your Windows Developer account has been activated (Phew).
2. Symantec Enterprise Code Signing Certificate
Now we will request a Symantec Enterprise Code Signing Certificate. Note that there is a cost associated with this.
Symantec recommend that you use Internet Explorer to request the Code Signing Certificate - it seems that other browsers can give difficulties with the Private Key (I can verify that I previously had difficulty using Chrome but good success with IE10/Windows 7 combination).
You MUST use the same browser (the same computer) to request the certificate and subsequently download it. If you make a mess out of this you will have to purchase a new certificate (although Symantec will refund you for the first one).
Follow this link
https://products.websecurity.symantec.com/orders/enrollment/microsoftCert.do
Enter your Symantec Publisher ID (from your Windows Developer Account). Also enter your email address.
Enter the required details (marked by red asterisk).
Accept the Symantec terms.
Accept the Microsoft terms and click to "Submit Order".
Accept the warning.
Your order has been accepted and you are given an order number.
Very quickly you will receive an email from Symantec thanking you for your order.
You will receive another email from Symantec. Read the instructions and follow the link to approve the request.
Finally you receive the mail informing you that your request has been approved. It also gives you instructions on downloading and installing the certificates.
Sent: 13/12/2013 13:22
To:
Subject: Your Enterprise Code Signing
Certificate Has Been Approved
-----------------------------
Congratulations!
Symantec has approved your request for an Enterprise Code Signing
Certificate.
ORDER NUMBER:
COMMON NAME:
Note: Your
Enterprise certificate is issued by a private Microsoft Root and CA, and is not
inherently trusted by your computer. Please ensure that you install and
trust the Root and CA certificates before installing your Enterprise certificate (newer Windows
operating systems will not allow you to install your Enterprise certificate
properly if the issuing chain is not already trusted).
STEP 1 – Install the Root certificate:
Click on the link
below and install the Root certificate. When prompted for where to
install the certificate, select the option to “Place
all certificates in the following store” (DO NOT accept the automatic
default) and select the “Trusted
Root Certification Authorities”
store.
STEP 2 – Install the CA certificate:
Click on the link
below and install the Intermediate certificate. When prompted for where
to install the certificate, select the option to “Place all certificates in the following store” (DO NOT accept the
automatic default) and select the “Intermediate Certification
Authorities” store.
STEP 3 – Install your Enterprise certificate:
Please use the
pickup link below to install your certificate. If using Windows 8 / IE 10 to
pickup your certificate, please put your browser into "compatibility
mode" first -- this is accomplished by clicking on the "ripped
page" icon to the right of the URL. Clicking the icon toggles this
mode.
Also visit the
Symantec Support Web site, where you will find a wide range of support tools to
help you:
Best Regards,
Please see the
following KB article for more information:
Download and install the Root Certificate (using the same browser and computer with which you made the request).
https://knowledge.verisign.com/library/VERISIGN/ALL_OTHER/Symantec_Enterprise_Mobile_Root_for_Microsoft.cer
Save and install the certificate.
Choose the correct store - Trusted Root Certification Authorities.
Review the settings and Finish.
Accept the Warning.
Download and install the Intermediate Certificate (using the same browser and computer with which you made the request).
https://knowledge.verisign.com/library/VERISIGN/ALL_OTHER/Symantec_Enterprise_Mobile_CA_for_Microsoft_Cert.cer
Save and install the cert.
Choose the correct store - Intermediate Certification Authorities.
Click to Finish the wizard.
Download and install the Enterprise Certificate (using the same browser and computer with which you made the request).
Configure browser settings for IE.
Follow the link in the email above (it will be specific to your request). The other links were general.
Accept the warning.
Confirmation that the Enterprise Certificate has been installed on your local PC.
Now we have to export the Enterprise Certificate so that we can use it in our ConfigMgr environment.
Open the Microsoft Management Console on your local PC (mmc). Select File > Add/Remove Snap-in.
Choose Certificates and select Add.
Choose "Computer account".
Choose "Local Computer".
Click OK to load the Certificates Snap-in.
Right click Certificates and choose "Find Certificates".
Type Symantec and click Find Now.
See the three installed certificates. Right click the Enterprise Certificate and choose to Export it.
Make sure that you export the private key.
Choose the .PFX format. Ensure that you "Include all certificates in the path".
You MUST password protect.
Specify a path for the exported .PFX file.
Finish the wizard.
The export has been successful.
3. Sign Company Portal
Next step - we need to download the Windows Intune Company Portal for Windows Phone and sign it with the Enterprise Certificate that we created in step 2 above. Note that you carry out all these steps on your local PC (I used a Windows 8.1 PC).
Download Company
Portal for Windows Phone here
Choose to download and save. Start the setup wizard.
Accept the Microsoft License Agreement.
Installation is complete.
Now download and install Windows
Phone 8 SDK (Software Development Kit) and Visual Studio 2012.
Reboot may be required to enable HyperV.
Have a look in the Windows Kits folder. See signtool.exe. This is the tool for signing apps.
Have a look in the Windows Intune Company Portal folder. See SSP.xap. This is your Company Portal app.
Copy signtools.exe, SSP.xap and your .PFX certificate to the XapSignTool folder.
Now open an Administrator Command Prompt and navigate to XapSignTool folder under your Microsoft SDK folder in Program Files (x86).
Issue the command
XapSignTool.exe Sign /f Nameofyourcertificate.pfx /p YourCertificatePassword SSP.XAP
Your Company Portal app (SSP.XAP) is now signed with your Enterprise Certificate.
See the properties of SSP.XAP.
4. Enable Windows 8 Phone
We have signed our Company Portal app and now must create a ConfigMgr application using our SSP.XAP file.
Copy the SSP.XAP file and .PFX Enterprise Certificate to your ConfigMgr Source folder.
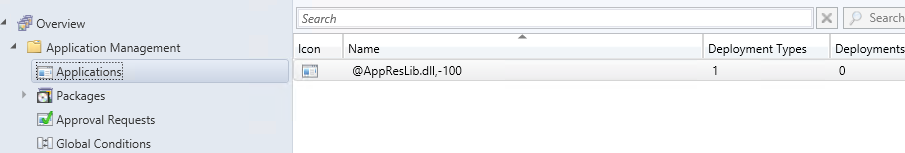
Navigate to Software Library > Application Management. Right click Applications and choose to create one.
Choose "Windows Phone app package *.xap"
Browse to your SSP.XAP file.
The file is interrogated by ConfigMgr and application information is imported.
Change the name if you wish.
Click next to continue.
Click Close to end the wizard.
The "Windows Intune Company Portal for Windows 8 Phone" app has been created.
Now, open the Windows Intune Subscription and choose to Enable Windows 8 Phone enrollment. Select your .PFX Enterprise Certificate and "Windows Intune Company Portal for Windows 8 Phone" app.
5. Test Windows 8 Phone device
You can now test with a Windows 8 Phone. However I don't have one. Luckily the Windows Phone SDK (Visual Studio 2012) has an emulator that I can use.
Note that if I was using Windows 8 I could just continue here. However the Visual Studio 2012 emulator does not work with Windows 8.1. I need to install the Visual Studio 2012 Update 4 first.
You can download it here
http://www.microsoft.com/en-us/download/details.aspx?id=39305
Download and install the VS update.
Launch Visual Studio 2012 (with update 4).
Select "New Project".
Choose Windows Phone.
Choose "Windows Phone OS 8.0".
Click on the green triangle to launch the emulator.
Scroll to the right.
Choose Settings.
Select "Company Apps".
Click "Add account"
Enter your email address (actually UPN - remember our AD configuration) and password. Note that you must be a member of the "Intune Users" ConfigMgr user collection.
Enter the server details
manage.microsoft.com
(If I previously created a DNS record for my domain to direct EnterpriseEnrollment to manage.microsoft.com then I would not need this step).
The account is being configured.
The account is verified and successfully added to the device. Make sure that "Install company app or hub" is checked.
The device is enrolled - whew.
See Company Portal. Launch the Portal.
You are asked to sign in to Intune. Use your email address and password again.
See the Apps which have been deployed to this user.
Note that company policies will now apply and the user will be forced to choose a PIN code.
See enrolled device.
Device details.